LTG Fogarty, Commander of ARCYBER, signed a memo this week authorizing a $20K per year for four year bonus ($80K total) for eligible cyber warrants.
DNS Over HTTPS
You may have noticed recently that Comcast and a number of ISPs have started to fight with Google and Mozilla after the makers of Chrome and Firefox announced that they were going to start support the use of DNS over HTTPS (DOH) and DNS Over TLS (DOT) recently
Identity Awareness, According to the DOD
Brought to you by the same group that thought that thought that Jeff and Tina were the way to get us to be cyber aware has now released their “Identity Awareness, Protection, and Management Guide”.
Computer Network Operations Development Program (CNODP) Class of 2023
Yesterday HRC released MILPER message 19-233 which announced applications for the Computer Network Operations Development Program (CNODP) class of 2023. For those of you not familiar with it, CNODP is the Army’s school for training future cyber tool developers. CNODP is comprised of the System and Network Interdisciplinary Program (SNIP), the Global Network Exploitation and Vulnerability Analyst (GNEVA) Development Program (GDP), and the Joint Cyber Development Program (JCDP).
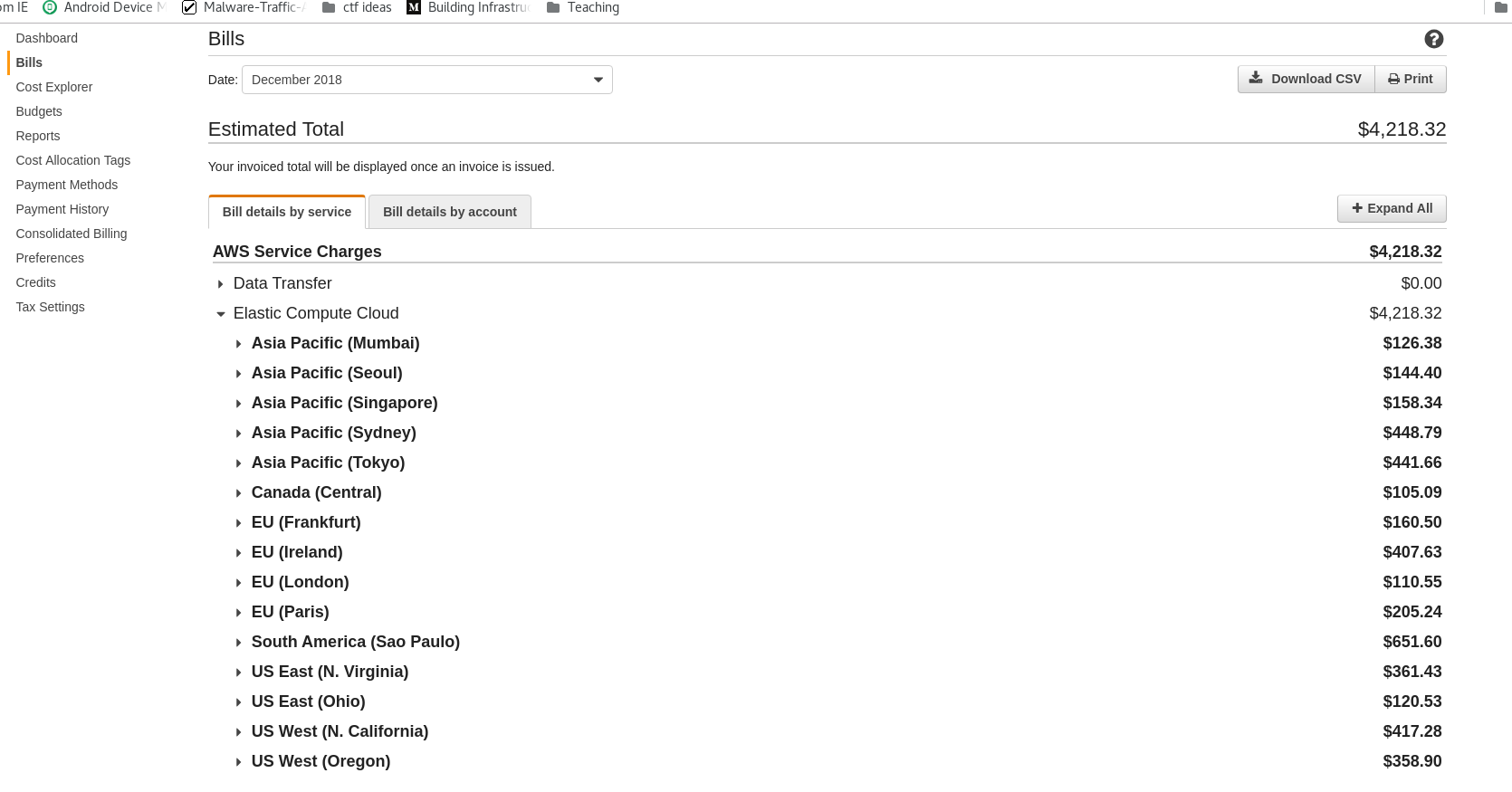
Hide Your Privates
So I learned a pretty tough lesson today. I was doing some research for a project at work (which was going to be the original topic of today’s post) on which required me to setup a SOCKs proxy through AWS. I logged onto AWS, configured a small instance and went to spin it up when I got an error message saying that I didn’t have permissions to do this.
Dec WOCS Selection Results
I know it’s a few days late (sorry, been busy) but I would like to welcome the newest group of 170As to join the Corps.
Black Friday Deals
Here’s one for my fellow learn-through-labs and CTF enthusiasts https://t.co/SOYl892PKy pic.twitter.com/EPg5cFp3lp
— Jessica ??? (@jessploit) November 21, 2018
Here are the current deals that I am tracking related to info sec and other general nerdery. Will update as I can. Here we go again! Pastebin – Lifetime Pro Acct. Deal: $19.95 (normally $49.95) Dates: Current – 11/27 Link: https://pastebin.com/pro?coupon=blackfri Source: https://twitter.com/pastebin/status/1064836723388149760 Shodan – Lifetime Deal: $5 (normally $49) Dates: 11/23 – 11/26 Link: »
Warrant Officer Promotions
For the first time in a very long time, the warrant officer promotion board results were actually released in the same FY as when the board actually met! First let me say congrats to everyone that was selected for promotion. Before I go into the numbers, let me preface this by saying that these numbers »
Computer Network Operations Development Program
Late last week HRC released MILPER message 18-264 which announced applications for the Computer Network Operations Development Program (CNODP). For those of you not familiar with it, CNODP is the Army’s school for training future cyber tool developers.
Honey Pots Get a Little Less Sticky
The other day a friend of mine shared a link to a new academic paper that was just released by a couple of researchers at the University of Cambridge. The team, Alexander Vetterl and Richard Clayton, wanted to see if they could create a technique to identify publicly accessible honeypots without having to actually interact with them.