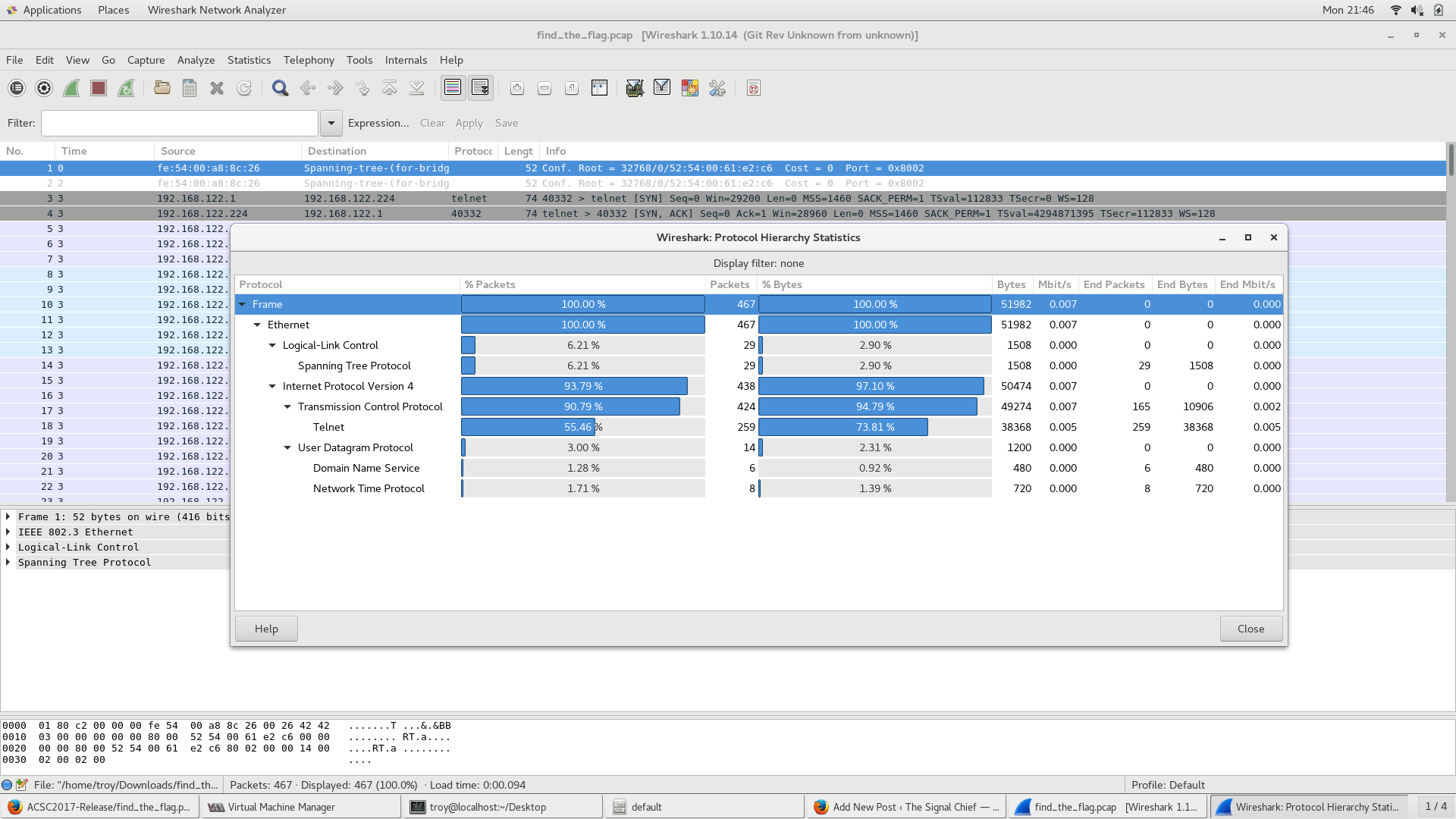
Another quick walk-through from ACSC5. This problem is called find_the_flag. Problem: Someone thought that using telnet was a good idea. Guess this should make your job a lot easier…..Find the flag
Congress Blames the Wrong Guy
A couple of days ago, I posted an article about some some possibly non-public military locations being discovered after fitness tracker company Strava put up a heat map of their users activity. In the 48 hours or so that has passed 9 Democratic members of congress wrote a letter to Strava asking for information. The letter makes a number of statements and asks questions that I think look to shift the blame of all of this on Strava instead of the military and the individuals who were wearing fitness trackers and publicly broadcasting their location information. I will go through a number of points and include my own response.
whats_my_password
Another quick walk-through from ACSC5. This problem is called whats_my_password.
Problem
What is that administrator’s password? Note: enter the flag in the format acsc2017{}
find_the_stack2
The is a follow-on to the first find_the_stack problem from ACSC5. This was originally supposed to be the third one in a series of challenges based on this problem but I had some problems with number two so this became number two.
find_the_stack
This is the first of what will hopefully be many walk-throughs from various CTF competitions I’ve competed/worked on. This first challenge is a simple one that I created for the 5th annual Army Cyber Skills Challenge.
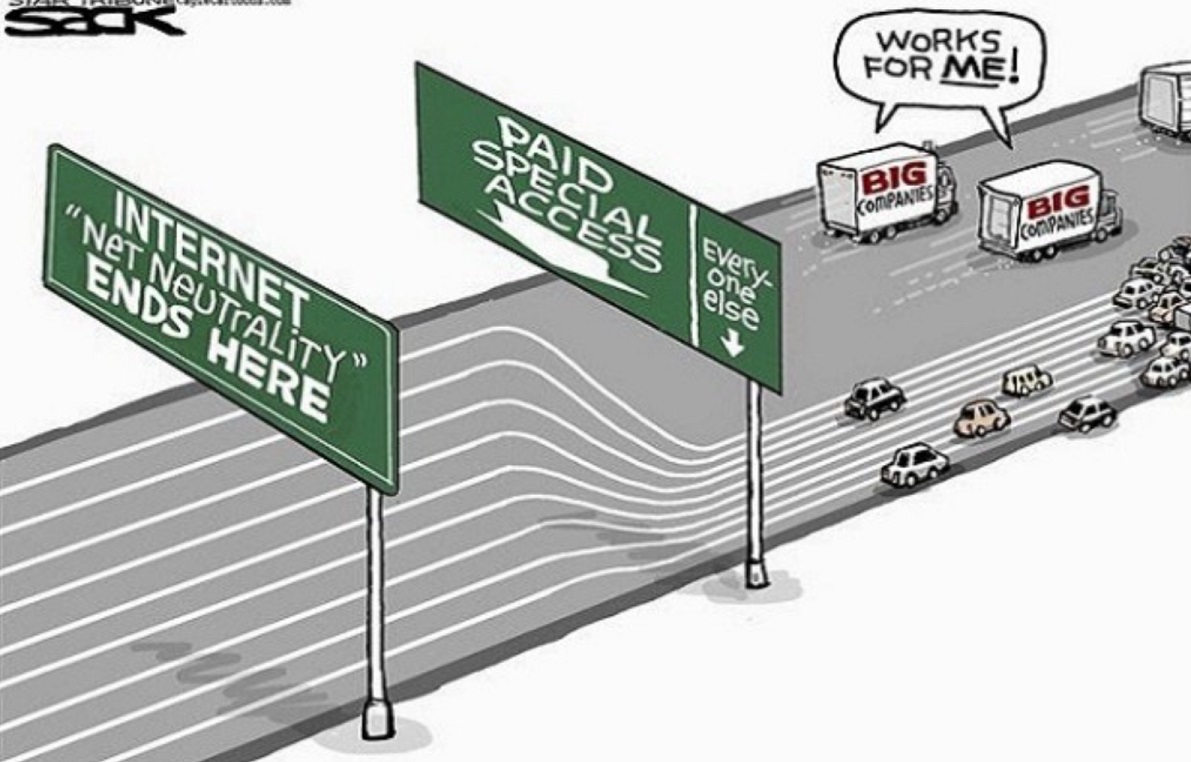
Net Neutrality
Earlier this week, the FCC, “lead” by Ajit Pai voted to repeal its policy of Net Neutrality. The policy was put into place in Feb 2015 after the FCC (at the time under the Obama administration) made the decision to classify ISPs as a public utility under Title II of the Telecommunications Act. For a lot of people (myself included for a while), this doesn’t make a lot of sense what any of this means so let me try to take a few minutes to explain (at least my understanding of it).
Cyber Direct Commisioning
This morning, I was going through the Army Times early bird and came across an article called Army offers direct commissions to boost cyber force. Talk about this came out initially a few months ago. Like many ideas, I think it’s a good idea but probably not one that is fully thought out.
November Warrant Officer Selection Results
So I know it’s a few days late (what can I say, I was getting ready for a turkey comma) but I wanted to take a minute to congratulate the Army’s newest cyber warrant officers (ya I’m still signal but I play cyber during the day). So with that being said congrats to:
Capture the Flags
Many of us remember playing capture the flag (CTF) back when we were kids. The idea was to divide into teams, try to sneak to the other teams side and capture their flag. Years later, this idea was expanded on when Playstation and XBox started putting together multiplayer games that had the same general idea. More recently, the idea has morphed once again with hacking and computer security related CTF competitions. Perhaps the most famous CTF is the annual Defcon CTF where participants from around the world work to qualify to take part in the event at the conference itself, but this is just one of countless CTF competitions that take place on nearly a daily basis.
Splunk .conf Day 2 and 3
So when I last left you guys I was attending Splunk .conf. My plan was to write each day but I quickly realized how long the day was when you included 9 hours of conference, plus commuting to and from DC each day so screw that.