My oldest kid wanted a Minecraft server for them and their friends, but I didn’t want to pay to run one 24/7. What should have been an easy project turned into a lot of discovery learning. Save yourself sometime and read this.
Firewall Testing with TRex
I recently had to do some throughput testing on a firewall using TRex. What should have been a pretty simple process honestly took a little bit of troubleshooting.
Requirements
I’ve been an engineer for a long time. In order to solve problems, my customer gives me requirements so that I can provide solutions. But the process breaks when the customer shortcuts the requirements process.
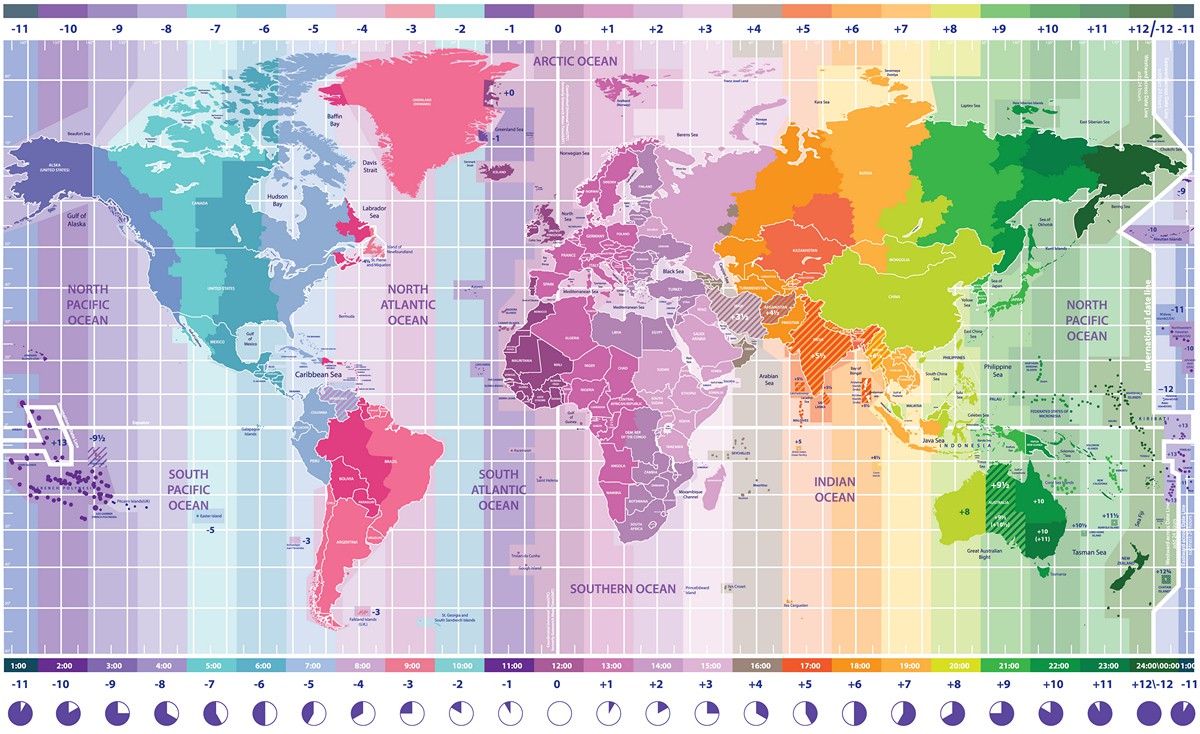
One More Time About Time
I’ve written about the importance of having accurate time before, and have always said that it can be difficult to keep a proper clock. I’ve always looked at it from a technical standpoint but a couple of days ago, one of my students sent me a video
and it caused me to look at the topic of time from a completely different perspective.
New Adventures
Today I am excited to announce that I have a new job! After spending the last year and a half or so at SEE, I’ve decided to make the move to SealingTech. While I love the team at SEE, SealingTech offered me a new adventure.
Workstation Setup
I’ve been doing dev work for years but have never taken the time to document how I like my setup which means every time I do it again, I have to figure it all out again.
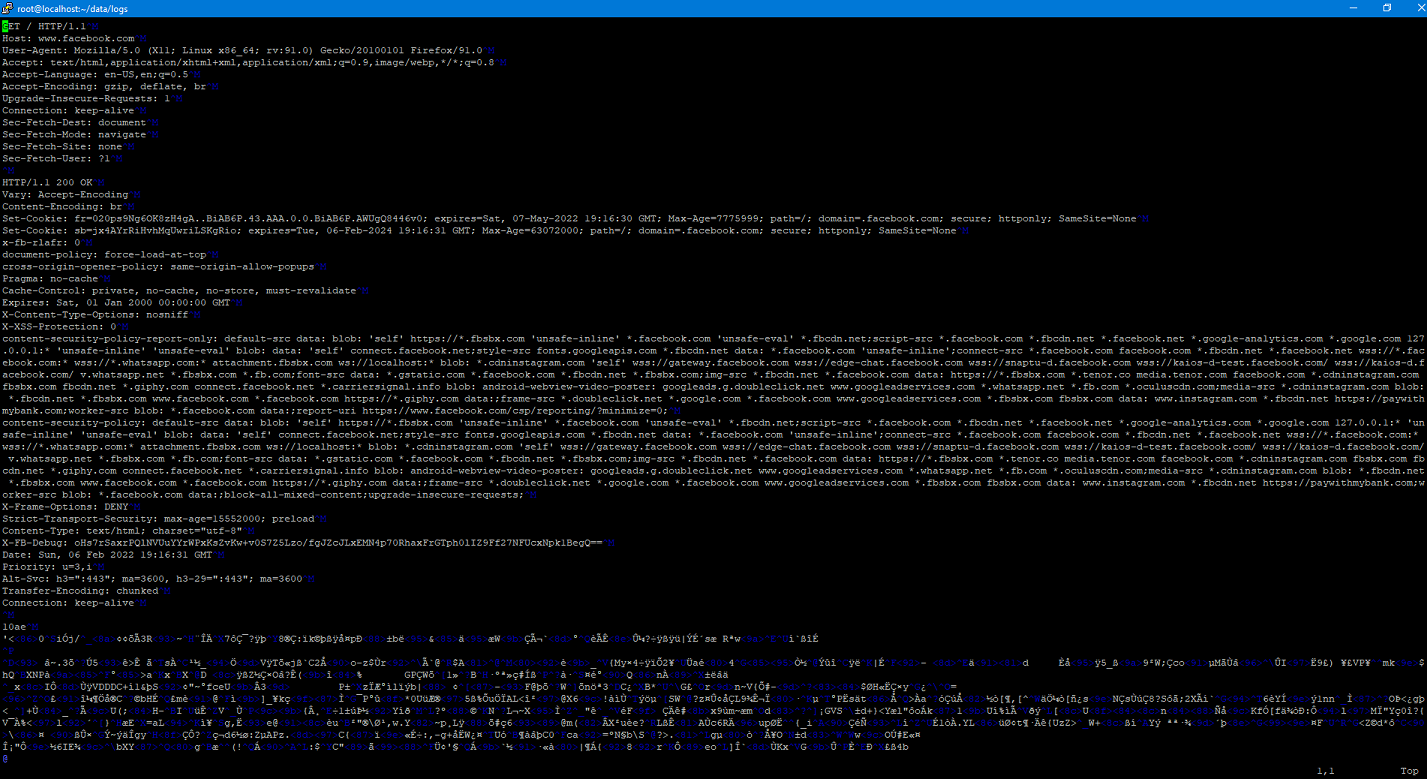
Implementing SSLSplit
A couple of weeks ago I talked about using SSLSplit to at as a proxy so that I could examine the mechanics of a Docker pull. I decided to go ahead a set up a purpose-built VM just for this so I could easily do this again in the future. I wanted to go ahead and document (and share) the steps that I went through for this.
Retirement Calculator 2022 Edition
A year or two ago I decided to create a retirement calculator to help me figure out my finances for when I was getting ready to retire. It occurred to me earlier today that I have done a poor job of keeping it current, so I decided to spend a few minutes and get it fully updated (I think) for 2022.
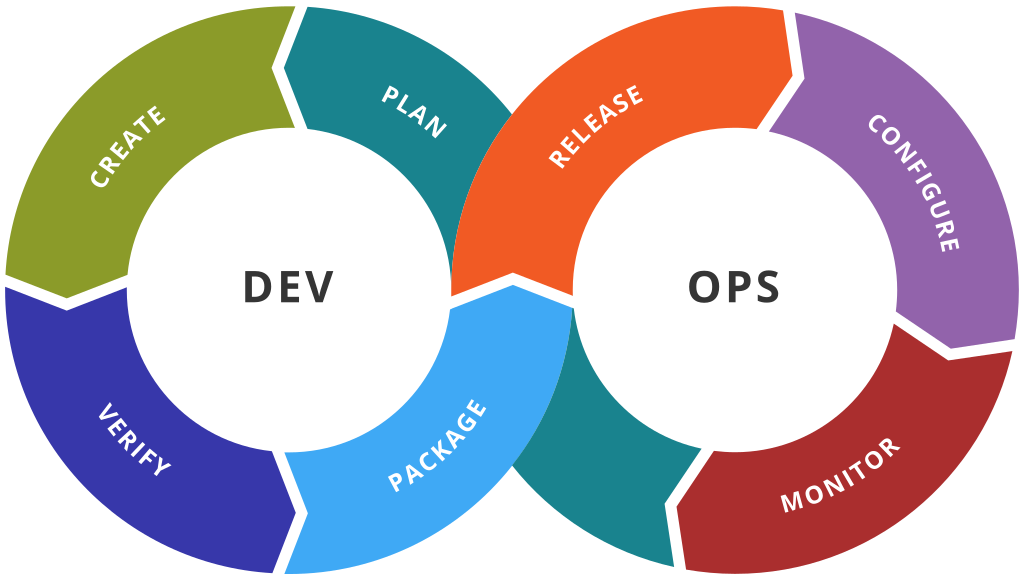
Mechanics of Docker Pull
Recently I’ve been in the process of building an offline repository of software for a project at work. The idea is that we’ll be able to completely install all required software completely disconnected from the Internet. When it got time to deal with containers…challenges abounded.
Retirement….One Year Later
Today marks one year since my last day wearing the uniform. Sure, my official retirement date wasn’t until Sept, but a lot of things have happened. In that time, we’ve continued to live through a pandemic, I’ve started a job, quit a job, and started another one, done a lot of work around the house, and been able to enjoy life a little bit.