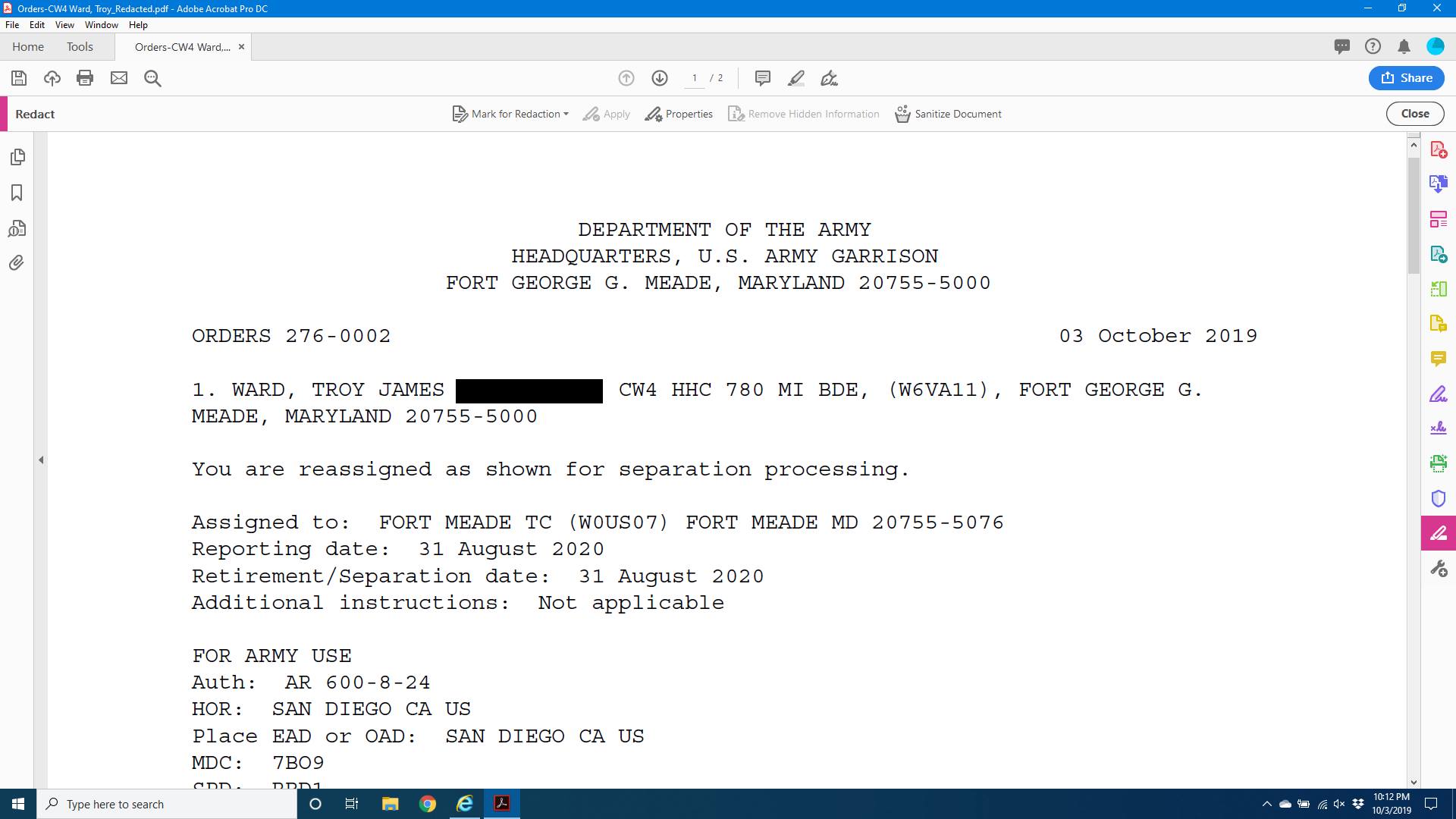
I am now 120 days away from starting my permissive TDY as I leave the Army after nearly 21 years. Part of that process is figuring out how much money I need to make.
Advent of Code – Day 2
Day 2 (only 13 days late) of Advent of Code was a throw-back to the Apollo moon landing…..Spoiler Inside.
Advent of Code – Day 1
Well I’m only 13 days late, but better late than never. I had some time to kill tonight and decided to finally jump on this year’s advent of code. Each day consists of 2 problems that you solve. So here goes Day 1…..Spoilers Inside
Recovering a RAID Disk
Many years ago I was looking for a network drive that I could attach to my home network to centrally save data. Life was good until a year or so ago when the NAS itself stopped working. I had used the drive for a variety of reasons, among them as a place to put all of our family photos.
Advent of Code
If you are looking for a fun way to work on your coding skills over the next 25 days or so I would encourage you to check out advent of code. This is a project run by Eric Wastle.
Defensible Security Architecture Certified
On Friday, I sat for the GIAC Defensible Security Architecture (GDSA) exam. The certification is brand new and is based on the SANS Sec 530 course. While I passed, it didn’t go the way I had planned
Cyber Warrant Bonus Follow-Up
My last post about the $80K bonus for Cyber Warrants got a lot of comments on Facebook. A lot of them focused on two key things, the kind of odd restrictions built around it (as far as timelines go), and then the fact that 255S were not included in it.
$80K Bonus For Cyber Warrants
LTG Fogarty, Commander of ARCYBER, signed a memo this week authorizing a $20K per year for four year bonus ($80K total) for eligible cyber warrants.
DNS Over HTTPS
You may have noticed recently that Comcast and a number of ISPs have started to fight with Google and Mozilla after the makers of Chrome and Firefox announced that they were going to start support the use of DNS over HTTPS (DOH) and DNS Over TLS (DOT) recently
All Good Things Must End
Well boys and girls after a lot of thinking, consideration, and discussion with my family, I’ve decided that it is time to call it a day with my career in the military.