A short update. I have officially been out of the Army for 16 days now and a lot has happened. I started my terminal leave back in mid-May, at the height of the Covid crisis. To say it wasn’t how I had planned to have my transition would be the understatement of the world.
Let’s Get Ready to Vote!
As I mentioned a week or so ago, we’re rapidly approaching the time that the military is able to most let our elected official know what we think. Below, I’ve compiled a chart of voting info.
Rights, Sorta Rights, and Not Rights
In case you haven’t heard, in 107 days, there is a small election that no matter what you believe in or who you plan on voting for, will have a direct impact on a variety of elements of your life for the next 2-6 years.
Retiring in a Rona World
Greetings from Fort Livingroom. I am now 35 days into my terminal leave (well 20 days PTDY and 15 days leave). I have decided to forego the “Freedom Beard” for right now (my wife threatened me with divorce) but my hair is rapidly approaching hippy level.
Making Use of Free Time
So since this whole COVID-19 thing started, I’ve had a lot of free time on my hands. Yes, I’ve suddenly become a teacher (I’m taking care of my oldest, while Liz takes care of our youngest) but I am only working at the office one week out of every three. That gives me a lot of time. I decided among other things to work on my Python (a lot). So I went back to the 2015 Advent of Code and just started going away. So here are the first five days of the 2015 Advent of Code.
Time To Sign Off
Yesterday I did something that has been nearly 21 years in the making; I finished my last working day in the Army. While I still have 2 weeks of out processing to complete, my time has come to an end. I will be the first to admit that this is a day I never thought I would see.
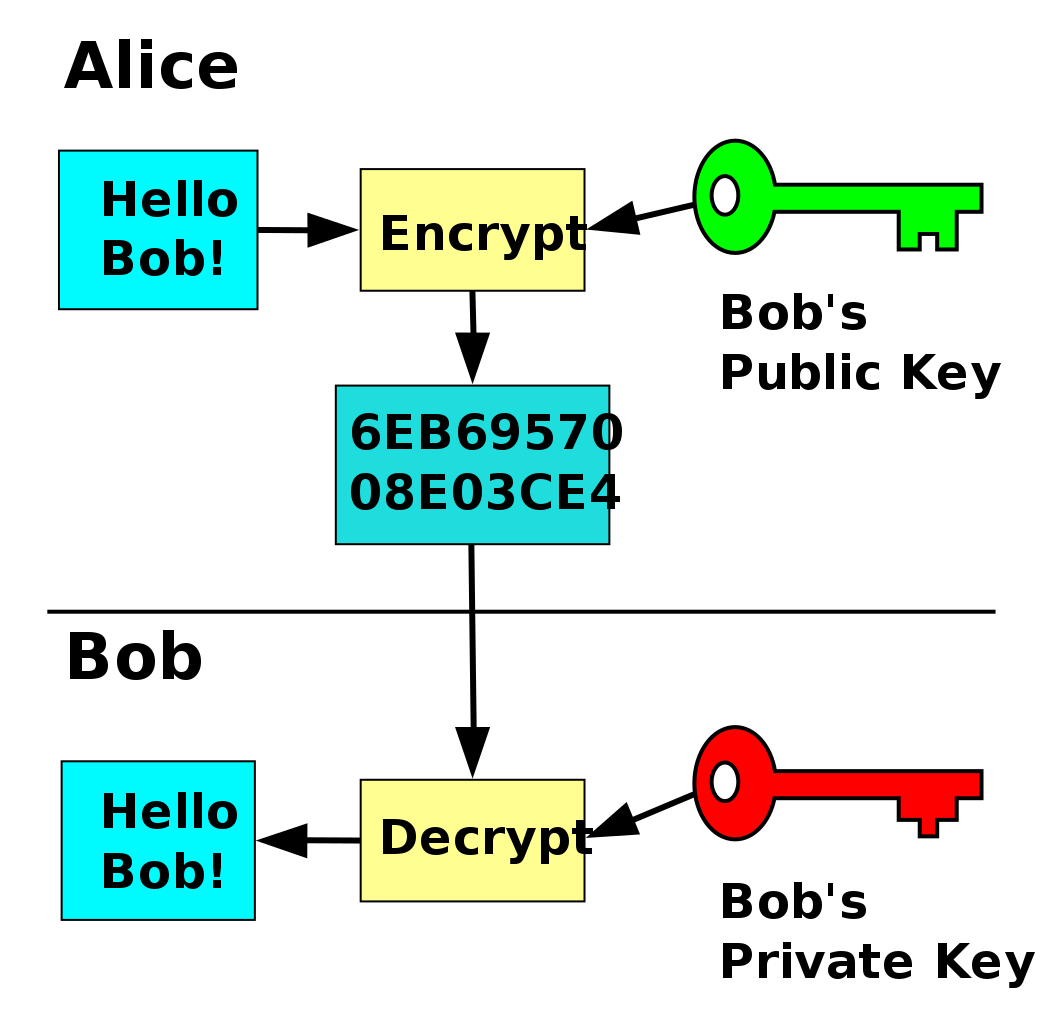
Asymmetric Encryption for Dummies
I’ve always found encryption interesting. While I’m not a mathematician I understand the basics generally. That statement mostly holds true when it comes to a symmetric encryption, but not so much when we start talking about asymmetric encryption.
Advent of Code – Day 4
So since we’ve had a little bit of free time lately, I’ve been doing some python scripting. The other day I decided to go back to Advent of Code and work on it a little bit more.
Transition Calculator – Part 2
So after receiving a lot of great feedback from people from the first version of the transition calculator, I decided to improve and rework parts of it. You can find the new version here.
Advent of Code – Day 3
Day 3 (only 62 days late) of Advent of Code was a huge pain in the ass but a lot of fun.