 Network Security
Network Security
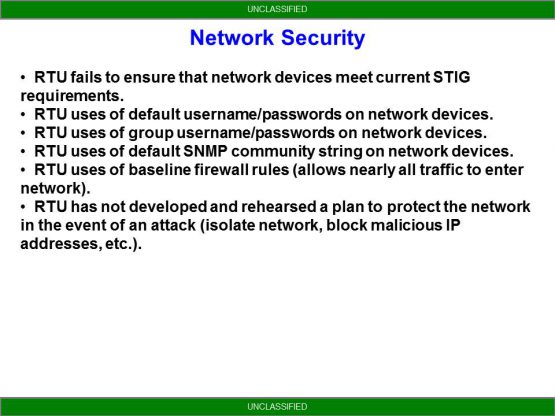
RTU fails to ensure that network devices meet current STIG requirements:
Have you ever heard of a STIG? Or know what it actually is? DISA has published a huge number of documents that work on a combined policy/technical level to secure just about anything IT related. These range from software to hardware to network devices and everywhere in between. They are updated regularly to keep up with current trends and compliance is actually mandated. Common sense would tell us that the various project managers who put together things like WIN-T, ABCS and the huge host of other systems on the network would be required to meet these STIG requirements before they field the systems but that is not always the case and there are often serious critical vulnerabilities that exist on baseline configurations. In other cases, a configuration covers a particular STIG assuming the Net Tech fills in the blanks.
RTU uses of default username/passwords on network devices:
While I will not post the default WIN-T username and password here for OPSEC if you use it you might as well be using the cisco default of cisco. The default username/password is there simply to be a place holder in the configuration. It is the Net Tech’s responsibility to CHANGE IT! That means not just the password, but use a different username as well. Why give an attacker half of the answer to the problem? Make sure that the password meets complexity requirements.
RTU uses of group username/passwords on network devices:
Along with using default username/passwords the next worse thing you can do is just a group username/password. In a perfect world, everyone would have their own password that is unique to each individual system. In reality that is not possible however we can come close. When I was first a Net Tech the JNNs each had TACACS+ loaded on their management system which made access control and logging of systems very easy. That has since gone away (a decision I completely disagree with) however you do have the tools to run a RADIUS server and authentication which is a close second. I plan on putting together a tutorial on setting up RADIUS another time but simple to say, it allows you to centrally create and manage individual logins for all of your users and restrict their access to particular devices. One last thing, it is critical to ensure that you have an emergency username/password on every device in the event that the device can’t contact your RADIUS server. Ensure that this username and password is highly secure because chances are, you’re going to use the same one on every device in the network.
RTU uses of default SNMP community string on network devices:
SNMP is an extremely powerful tool that makes our jobs a hell of a lot easier. But there are two important things to remember about it. 1. Even read only access can give an attacker some pretty important information about the network that you would probably rather them not have and 2. With read/write access, an attacker can do pretty much whatever they want with your router which is why it is important to secure it. The baseline configs for WIN-T use SNMP v2 which is widely acknowledged as being weak and fails to meet the current STIG. SNMP v3 on the other hand is pretty secure but not used in WIN-T by default. While the baseline configs to WIN-T does specify a default community (fortunately it’s not “Public”) it is only unique to a particular division which means that every system in the entire division has the same community strings. In my own humble opinion, each Brigade should take it upon themselves to come up with a unique community string.
RTU uses baseline firewall rules (allows nearly all traffic to enter the network):
Have you ever bothered to look through your firewall configs? Most people haven’t because it’s something that is not easily understood. I will not go into detail in this post (more to come though) but if you think your firewall is secure, I will say you are sorely mistaken assuming you’re using the default configs. More to follow in a later post.
RTU has not developed and rehearsed a plan to protect the network in the event of an attack (isolate network, block malicious IP addresses, etc.):
For anyone who hasn’t been through NTC (or JRTC) in the last 2 years or so, you may not know but we have a cyber red team that comes out and takes part in each rotation. As a very basic overview, they attempt to replicate an inside threat that is sympathetic/working with the enemy force (think Snowden or Manning). While it is not expected of the unit (nor should it be in my own personal opinion given your lack of training, manning, or expertise) to keep the attackers out, what we are much more interested in is seeing how the unit reacts once they recognize an attack. This is something that needs to be thought out beforehand, tested, and rehearsed. I have seen units completely disrupt all communications because they didn’t really understand what they were doing in an attempt to block an attacker.
